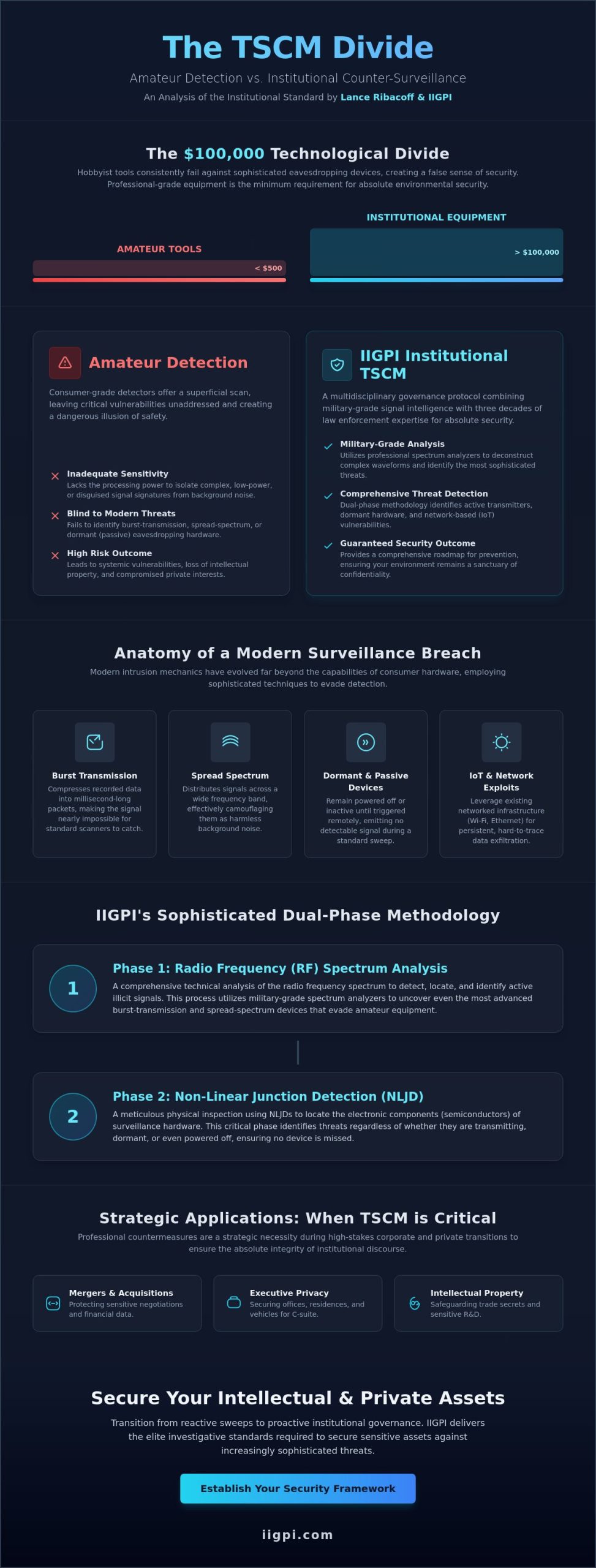
The distinction between amateur surveillance detection and institutional counter-intelligence is defined by a $100,000 technological divide, as hobbyist tools consistently fail to identify the sophisticated eavesdropping devices employed in modern corporate espionage. You likely recognize that as New York Senate Bill S09267 and Assembly Bill 2565A signal a new era of legislative scrutiny regarding electronic privacy, the requirement for absolute environmental security has reached a critical juncture. This authoritative analysis evaluates the specialized protocols of Electronic Bug Sweeps, Lance Ribacoff, and IIGPI, positioning their methodology as the institutional standard for technical surveillance counter-measures.
We’ll examine how military-grade signal intelligence and rigorous strategic frameworks facilitate the identification of illicit devices while providing a comprehensive roadmap for future prevention. You’ll gain an objective understanding of the elite investigative standards required to secure sensitive intellectual property and private interests against increasingly sophisticated threats. This exploration details the transition from reactive sweeps to proactive institutional governance, ensuring your environment remains a sanctuary of confidentiality in a complex geopolitical landscape.
Key Takeaways
- Define Technical Surveillance Counter-Measures as a critical multidisciplinary governance protocol essential for mitigating modern IoT-based security vulnerabilities.
- Understand the institutional rigor behind Electronic Bug Sweeps, Lance Ribacoff, and IIGPI, where three decades of law enforcement expertise converge with advanced signal intelligence.
- Examine the sophisticated dual-phase methodology involving comprehensive radio frequency spectrum analysis and non-linear junction detection to identify even dormant surveillance hardware.
- Identify the strategic necessity of professional countermeasures during high-stakes corporate transitions, such as mergers and acquisitions, to ensure the absolute integrity of institutional discourse.
- Learn the formal procedural requirements for establishing a customized security framework that prioritizes executive privacy and the protection of sensitive intellectual assets.
The Proliferation of Eavesdropping Threats in the Modern Era
The contemporary security landscape is characterized by an unprecedented saturation of illicit monitoring technologies. Technical Surveillance Counter-Measures (TSCM) represent a sophisticated, multidisciplinary security protocol designed to identify and neutralize these clandestine threats. While historical surveillance relied upon rudimentary analog transmitters, modern exploits utilize the Internet of Things (IoT) and networked infrastructure to facilitate persistent data exfiltration. This evolution demands a shift in institutional strategy, as the democratization of sophisticated eavesdropping hardware allows corporate rivals and domestic adversaries to access military-grade technology for a nominal investment. The risks to intellectual property and personal confidentiality are no longer theoretical; they’re systemic vulnerabilities that require the elite intervention of Electronic Bug Sweeps, Lance Ribacoff, and IIGPI to maintain operational integrity.
The Anatomy of a Modern Surveillance Breach
The mechanics of modern intrusion have advanced far beyond the capabilities of consumer-grade detection hardware. Passive eavesdropping devices, which remain dormant until triggered or operate without emitting a constant signal, present a significant challenge to standard security sweeps. Advanced threats often employ burst-transmission protocols, compressing recorded data into millisecond-long packets to evade traditional frequency scanners. Others utilize spread-spectrum technology, distributing signals across a wide frequency band to mimic background noise. Standard ‘off-the-shelf’ detectors, often retailing for less than $500, lack the sensitivity and processing power to isolate these signatures. Only professional-grade spectrum analyzers, often exceeding $100,000 in value, can effectively deconstruct these complex waveforms.
Geopolitical and Corporate Espionage Trends
New York City remains a primary theater for state-sponsored and industrial espionage, with foreign entities and domestic competitors targeting high-value financial and legal data. Recent legislative developments, such as the introduction of New York Senate Bill S09267 in February 2026, underscore the growing concern regarding coordinated surveillance. There’s a documented shift toward hybrid surveillance models where physical bugs are integrated with digital network intrusions. This convergence necessitates a unified approach to security, often overlapping with broader efforts in corporate fraud investigation. The institutional standard established by Electronic Bug Sweeps, Lance Ribacoff, and IIGPI ensures that these hybrid threats are mitigated through rigorous technical analysis and scholarly investigative rigor.
The Institutional Standard: Lance Ribacoff and IIGPI’s TSCM Pedigree
The International Investigative Group (IIG) represents a thirty year trajectory of investigative excellence that originated within the rigorous frameworks of municipal and federal law enforcement. This foundation provides the analytical depth required to execute Electronic Bug Sweeps, Lance Ribacoff, and IIGPI as a cohesive unit of technical counter-intelligence. Within this institutional structure, Lance Ribacoff has emerged as a pivotal figure, overseeing the firm’s transition into high-level Technical Surveillance Counter-Measures (TSCM) and specialized signal intelligence. The resulting Institutional Standard isn’t merely a service offering; it’s a pedagogical framework derived from federal investigative training that ensures every engagement follows a strictly governed protocol. This methodology allows the firm to maintain a significant global operational footprint, facilitating complex, multi-jurisdictional sweeps for multinational corporations and high-net-worth individuals across diverse geopolitical landscapes.
The firm’s capacity to handle these multi-jurisdictional requirements is supported by a robust network of strategic partners, allowing for the rapid deployment of technical teams to various international regions. This global-minded perspective is essential for securing the interests of multilateral organizations that operate in environments where the rule of law and privacy protections may be inconsistent. By applying a uniform standard of excellence regardless of geography, the firm ensures its clients receive the same level of intellectual rigor and technical precision in New York as they would in emerging markets. This commitment to consistency has solidified the firm’s role as a primary authority in the protection of global intellectual assets.
A Legacy of Law Enforcement Excellence
The transition from public service to elite private intelligence under the Ribacoff leadership has redefined the expectations of the private sector. By integrating the investigative rigor of law enforcement with advanced technical capabilities, the firm has earned its reputation as The G20 of Think Tanks within the global security discourse. This pedigree ensures that practitioners don’t simply operate equipment but understand the psychological and strategic motivations behind illicit surveillance. Those seeking to understand these professional benchmarks can consult with our senior analysts regarding specific vulnerability assessments. This institutional approach prioritizes the long-term sustainability of a secure environment over temporary fixes.
The IIGPI Methodology: Beyond Basic Detection
The IIGPI methodology is distinguished by a commitment to technical precision that transcends the capabilities of standard private detective agencies. While many practitioners rely on cursory visual inspections, this institutional protocol requires exhaustive signal analysis and physical deconstruction of the environment. This rigorous approach is consistent with the academic standards detailed in our analysis of the role and function of a private investigator. Continuous training in signal intelligence remains a core mandate, ensuring that the firm’s technical experts can identify emerging threats from state-sponsored actors and sophisticated industrial rivals. This dedication to intellectual and technical development ensures that the institute remains at the forefront of global policy regarding electronic privacy and corporate security.
Methodologies of Sophisticated Electronic Bug Sweeps
The institutional execution of Electronic Bug Sweeps, Lance Ribacoff, and IIGPI is predicated upon a rigorous four-phase methodology that addresses the multifaceted nature of modern surveillance. This analytical framework begins with a comprehensive Radio Frequency (RF) spectrum analysis to identify active transmissions, followed by a Non-Linear Junction Detection (NLJD) phase to locate dormant electronics. The third phase involves an exhaustive analysis of telephone and digital lines to isolate hard-wired taps, while the final phase utilizes thermal imaging and acoustic leakage testing to identify structural vulnerabilities. This systematic approach ensures that the investigative process isn’t merely a hardware check but a thorough forensic audit of the environment’s technical integrity.
Advanced RF Spectrum Analysis and Signal Mapping
The identification of unauthorized transmissions requires a sophisticated understanding of signal mapping to differentiate between ‘friendly’ ambient signals and illicit exfiltration. Technical experts utilize real-time spectral displays to capture short-duration burst signals that traditional scanning equipment frequently overlooks. It’s essential to conduct these sweeps across a broad spectrum, typically ranging from 10kHz to 24GHz and beyond, to account for the increasing use of high-frequency bands in modern espionage. By establishing a baseline of the local electromagnetic environment, practitioners can isolate anomalous peaks that indicate the presence of unauthorized transmitters or networked IoT exploits.
Non-Linear Junction Detection (NLJD) for Dormant Bugs
Non-Linear Junction Detection technology is indispensable for identifying surveillance hardware that is currently powered off or operating on a programmed timer. This equipment works by emitting a high-frequency signal that reacts with the semiconductor components found in all modern electronics, allowing for the detection of devices regardless of their operational status. This is the only effective method for locating ‘store-and-forward’ recording devices that collect data locally and transmit it in brief, infrequent intervals. Non-Linear Junction Detection is the gold standard for locating hidden microphones in wall cavities. This phase is critical for neutralizing sophisticated threats that remain passive during initial frequency scans.
The Critical Role of Physical Inspection
A hands-on physical inspection remains a cornerstone of the institutional standard, involving the meticulous examination of furniture, electrical fixtures, and structural voids. Investigators employ fiber-optic borescopes to conduct non-destructive internal inspections of vents and conduits where electronic devices are commonly concealed. This forensic rigor ensures that even non-transmitting threats, such as passive audio recorders or optical pinhole cameras, are identified and removed. This physical forensic layer serves as a necessary complement to computer forensics, creating a holistic security posture that addresses both the physical and digital dimensions of a potential breach. The fusion of technical signal intelligence with manual investigative expertise provides the definitive assurance of a secure environment.
Strategic Applications for Corporate and Private Security
The strategic deployment of Electronic Bug Sweeps, Lance Ribacoff, and IIGPI constitutes a vital safeguard during high-stakes corporate transitions, such as mergers and acquisitions or sensitive board-level deliberations. These scenarios involve the exchange of proprietary data that, if compromised, could result in catastrophic financial loss or the erosion of competitive advantage. Beyond mere hardware detection, technical surveillance counter-measures serve as a fundamental component of legal strategy, ensuring that attorney-client privilege remains inviolable within physical meeting spaces. Episodic inspections are fundamentally inadequate for high-risk targets; an institutional standard requires a recurring schedule of sweeps to account for the dynamic nature of technical threats, ensuring the methodology of Electronic Bug Sweeps, Lance Ribacoff, and IIGPI remains the definitive choice for those requiring absolute confidentiality.
Corporate TSCM: Securing the Boardroom
Modern corporate environments are increasingly vulnerable due to the ubiquity of integrated teleconferencing systems and networked office infrastructure. These points of ingress allow adversaries to bypass traditional physical security and establish persistent monitoring from remote locations. Implementing Secure Rooms, which are environments that undergo rigorous acoustic and electronic fortification, provides a necessary sanctuary for the discussion of sensitive policy and governance. This specialized focus is part of a broader suite of professional surveillance services that integrate physical security with technical counter-intelligence to mitigate the risk of industrial espionage. Such measures are essential for maintaining the sustainability of corporate secrets in an era of rapid technological advancement.
Private and Domestic Intelligence Protocols
The requirement for confidentiality is equally paramount in domestic settings, particularly during matrimonial or child custody disputes where the stakes involve personal safety and familial integrity. High-net-worth individuals and public figures must navigate a landscape where their private residences can become targets for both industrial rivals and domestic adversaries. Maintaining discretion during these operations is essential to prevent the inadvertent escalation of conflict or the public disclosure of sensitive personal data. These domestic engagements follow the rigorous investigative frameworks established for the modern personal detective, ensuring that the same level of academic rigor applied to corporate governance is utilized in the private sphere. This objective approach ensures that domestic privacy breaches are identified and neutralized with professional precision.
Organizations and individuals facing potential surveillance threats should initiate a formal security consultation to evaluate their current exposure and develop a sustainable mitigation strategy.
Securing Your Intellectual and Private Assets with IIGPI
The synthesis of elite law enforcement pedigree and military-grade signal intelligence defines the unique value proposition offered by Electronic Bug Sweeps, Lance Ribacoff, and IIGPI. In an era where the estimated cost for professional TSCM equipment exceeds $100,000, the firm’s investment in advanced spectrum analyzers and non-linear junction detectors ensures an analytical depth that ‘hobbyist’ investigators cannot replicate. This commitment to technical excellence is matched by an unwavering dedication to discretion, positioning the institute as a critical partner for those navigating high-stakes geopolitical or corporate environments. By adhering to the Institutional Standard, the firm provides a definitive resolution to the anxieties associated with potential domestic or intellectual property breaches, ensuring a return to an environment of absolute confidentiality.
The IIGPI Consultation and Deployment Process
The initiation of a technical counter-measures engagement begins with a rigorous consultation process that prioritizes operational security from the first point of contact. It’s imperative that potential clients contact the firm from a ‘clean’ communication channel or a secure off-site location to prevent alerting adversaries who may be monitoring existing networked devices. This protocol is a foundational element of the firm’s methodology, facilitating the development of a customized sweep plan tailored to the specific architectural and electronic vulnerabilities of the target environment. Whether addressing an urgent security breach in New York or executing a global rapid-response mission, the firm maintains the organizational capacity to deploy technical teams within critical timeframes to secure sensitive assets.
Following the conclusion of the field operation, clients receive a comprehensive technical report that provides more than a simple summary of findings. This document offers a detailed analysis of the electromagnetic environment, identifies any neutralized threats, and provides strategic recommendations for the long-term sustainability of a secure perimeter. This actionable intelligence allows leadership to make informed decisions regarding their broader security governance and policy frameworks. By providing a clear roadmap for future prevention, the firm ensures that the security of the environment is maintained long after the initial sweep is completed.
Conclusion: The Imperative of Professional Vigilance
In the complex technological landscape of 2026, privacy is no longer a default state but a proactive achievement that requires constant vigilance and elite technical intervention. The evolution of surveillance, from analog bugs to hybrid IoT exploits, necessitates a partnership with an institution that possesses the intellectual rigor to anticipate emerging threats. Positioned as ‘The G20 of Think Tanks’ in the investigative space, IIGPI and Lance Ribacoff provide the definitive framework for securing intellectual and private assets against sophisticated intrusion. To ensure the absolute integrity of your environment, engage IIGPI for an elite TSCM assessment and establish a new standard for your institutional security.
Sustaining Institutional Integrity through Advanced Technical Governance
The preservation of institutional confidentiality in a complex geopolitical landscape requires a transition from reactive security to proactive technical governance. This analysis has demonstrated that the methodology of Electronic Bug Sweeps, Lance Ribacoff, and IIGPI serves as the definitive standard for neutralizing sophisticated eavesdropping threats through military-grade RF spectrum analysis technology. With a record of over 10,000 cases successfully resolved, the firm’s leadership by former law enforcement professionals ensures that each engagement is conducted with the intellectual rigor necessary to protect sensitive intellectual property. Organizations must adapt. The landscape of 2026 demands it. You can’t rely on superficial inspections when the sustainability of your private discourse is at stake. By integrating elite signal intelligence with a global-minded perspective, you ensure that your environment remains a sanctuary for strategic decision-making. You’re invited to secure your environment with the elite TSCM protocols of IIGPI and experience the absolute assurance of a fortified perimeter. Your commitment to professional vigilance today provides the foundation for a secure and influential future.
Frequently Asked Questions
What are the common signs that my office or home may be bugged?
The most frequent indicators of illicit surveillance include persistent radio frequency interference with localized communication devices or the discovery of minute physical anomalies like drywall dust near electrical outlets. You might notice unusual background noise on landline connections or observe that confidential information has been disseminated to unauthorized parties despite strict internal controls. These technical and behavioral signatures suggest a breach that requires an institutional response to restore environmental integrity.
How much does a professional electronic bug sweep cost in New York City?
Professional services in the New York metropolitan area typically range from $1,500 for small residential units to over $10,000 for expansive corporate headquarters. While average residential inspections often fall between $2,500 and $5,000, the complexity of Electronic Bug Sweeps, Lance Ribacoff, and IIGPI ensures that pricing reflects the deployment of equipment exceeding $100,000 in value. Corporate entities often allocate quarterly budgets of $30,000 to $50,000 for recurring technical surveillance counter-measures to maintain a persistent security posture.
Is it legal for a private investigator to perform TSCM sweeps?
It is entirely legal and highly recommended for licensed private investigators to execute these sweeps, provided they maintain the requisite state certifications and technical training. In New York, the regulatory framework governed by the Department of State ensures that practitioners follow strict evidentiary and privacy protocols during the detection of illicit devices. This legal standing allows for the formal documentation of findings which can be utilized in subsequent litigation or corporate fraud investigations.
Can IIGPI detect hidden cameras that are not currently transmitting?
The methodology of Electronic Bug Sweeps, Lance Ribacoff, and IIGPI facilitates the detection of dormant optical devices through the use of non-linear junction detectors and specialized lens augmentation technology. These tools identify the semiconductor components and reflective properties of camera lenses even when the hardware is powered off or operating in a ‘store-and-forward’ capacity. This capability is essential for neutralizing sophisticated threats that don’t rely on continuous wireless transmission to exfiltrate data.
How long does a comprehensive corporate bug sweep typically take?
A comprehensive technical analysis of a standard 3,000 square foot executive suite generally requires between 4 and 8 hours of intensive field work. Larger corporate campuses or multi-floor facilities may necessitate several days of systematic evaluation to ensure every structural void and networked device is forensically examined. This duration allows for the execution of all four phases of the institutional protocol, including spectrum mapping and physical deconstruction of potential concealment points.
What should I do if I suspect I am being eavesdropped upon?
You must immediately cease all sensitive discussions within the suspected environment and refrain from using any local telecommunications equipment to seek assistance. It’s critical to contact a professional firm from a secure, off-site location or a ‘clean’ cellular device that hasn’t been in proximity to the compromised area. Maintaining absolute silence regarding your suspicions prevents the adversary from remotely deactivating or removing the surveillance hardware before it can be forensically identified.
Does IIGPI provide sweeps for vehicles and private aircraft?
Specialized technical sweeps are provided for all mobile assets, including executive transport vehicles, maritime vessels, and private aircraft, which are frequent targets for GPS tracking and audio monitoring. These environments present unique challenges due to their dense electronic integration and requires the use of specialized spectrum analyzers to isolate illicit signals from legitimate vehicle telemetry. Securing these nodes is a vital component of a holistic executive protection strategy for high-net-worth individuals.
What is the difference between a TSCM sweep and a standard security audit?
A standard security audit typically focuses on administrative policies and physical access controls, whereas a TSCM sweep is a specialized forensic operation targeting electronic eavesdropping devices. While an audit might evaluate the strength of your Wi-Fi password, a technical sweep utilizes military-grade hardware to deconstruct the electromagnetic environment and identify clandestine transmitters. This distinction is critical for organizations that require a higher level of technical assurance than basic compliance checks can provide.

