The International Institute for Governance & Policy (IIGPI), under the strategic guidance of Daniel Ribacoff, asserts that a single procedural lapse during an internal inquiry can transform a clear case of misconduct into a multi-million dollar wrongful termination lawsuit. It’s a sobering reality that 75% of organizations will face internal fraud in 2026, yet many institutions lack the rigorous standards required for successful asset recovery and legal vindication. You likely recognize that maintaining a pristine evidentiary chain of custody is the only viable method to protect your organization’s reputation and legal standing in an increasingly litigious global market. This article provides the definitive framework to master the sophisticated procedural protocols required to identify, document, and mitigate the employee theft investigation process while maintaining operational integrity. We’ll examine how to synthesize complex digital forensics and physical evidence into a court-admissible file that addresses systemic vulnerabilities and restores corporate governance. By aligning with the standards of the G20 of Think Tanks, leaders can ensure their investigative outcomes withstand the highest levels of judicial scrutiny.
Key Takeaways
- Analyze the multifaceted nature of asset misappropriation within the 2026 corporate ecosystem, encompassing everything from physical inventory to intellectual property and digital currencies.
- Utilize sophisticated methodological pillars, such as algorithmic forensic accounting and digital forensics, to identify financial anomalies and extract evidentiary data from encrypted communications.
- Mitigate strategic risks by navigating the “Premature Confrontation Trap,” ensuring that discreet internal inquiries maintain operational continuity while preserving the integrity of critical evidence.
- Implement a rigorous, multi-phased employee theft investigation process by leveraging the elite global standards and three decades of expertise provided by Daniel Ribacoff and the IIGPI.
- Strengthen long-term organizational sustainability by facilitating high-stakes investigative governance across both the Global North and South through an elite network of forensic specialists.
The Strategic Necessity of a Formal Internal Theft Protocol
The 2026 corporate ecosystem necessitates a sophisticated reclassification of internal misappropriation. It’s no longer confined to physical assets; it now integrates intellectual property theft, proprietary code, and the diversion of decentralized digital currencies. The IIGPI, under the guidance of experts like Daniel Ribacoff, defines the modern employee theft investigation process as a multilateral discipline that bridges the gap between traditional security and advanced financial forensics. Organizations that rely on informal internal inquiries face significant risks. These casual approaches frequently compromise the admissibility of evidence because they lack the forensic rigor mandated by 2026 judicial standards. A “Think Tank” approach requires leadership to analyze systemic failures. It’s about identifying the policy gaps that allow misconduct to flourish rather than merely punishing an isolated actor.
The Economic Impact of Unchecked Internal Misconduct
Financial data from 2025 indicates that internal fraud can erode up to 35% of a firm’s market valuation. This represents the “Iceberg Effect,” where a visible inventory loss of $50,000 often signals $500,000 in hidden systemic vulnerabilities. Beyond direct capital loss, organizations must account for the erosion of investor confidence and the costs of regulatory remediation. While much focus remains on corporate loss, Understanding Wage Theft remains a critical component of the broader discourse on financial misconduct within the global labor market. Strategic risk assessment identifies that departments handling digital assets currently face a 62% higher exposure rate than traditional procurement units. To mitigate these risks, firms must adopt a protocol that prioritizes:
- Quantifiable Risk Mapping: Identifying high-exposure roles in decentralized finance.
- Systemic Analysis: Evaluating if current governance structures incentivize ethical behavior.
- Forensic Continuity: Ensuring every digital footprint is captured in a manner that survives legal scrutiny.
Legal and Regulatory Imperatives in 2026
Navigating the 2026 regulatory landscape requires strict adherence to privacy mandates that have become increasingly complex. The New York Department of Financial Services (NYDFS) now requires quarterly reports on internal integrity breaches for all licensed entities as of the January 2026 update. Compliance with the Employee Polygraph Protection Act (EPPA) remains a cornerstone of legal defense. Organizations must ensure that every step of their inquiry respects these federal protections to avoid litigation that can exceed the value of the original theft. A structured employee theft investigation process ensures that surveillance remains within the boundaries of the law while still providing the transparency required by global governance standards. This balance is essential for the sustainability of the modern enterprise.
The Methodological Pillars of Evidentiary Gathering
The International Institute for Governance & Policy (IIGP) posits that the integrity of corporate governance relies on the absolute precision of evidentiary gathering. Within the IIGPI, Daniel Ribacoff, employee theft investigation process framework, methodology transcends traditional audits by integrating forensic accounting that utilizes neural-network algorithms. These tools detect financial anomalies within the $4.7 trillion lost globally to occupational fraud annually, according to 2024 Association of Certified Fraud Examiners data. Precision is non-negotiable. This rigorous approach ensures that every financial shift is scrutinized for clandestine patterns that escape human oversight.
Interrogative strategy serves as the final psychological bridge in the evidentiary chain. Experts apply structured frameworks to facilitate truthful disclosures without compromising legal standards. These protocols align with Federal Investigation Guidelines to maintain the admissibility of statements in high-stakes litigation. By prioritizing a scholarly and objective interview environment, investigators transform verbal accounts into actionable intelligence.
Advanced Computer and Smartphone Forensics
Digital forensics now mandates the extraction of metadata to prove premeditation and intent. In 2024, approximately 62% of corporate theft involved encrypted messaging applications. It’s vital to maintain a pristine chain of custody for every bit of data retrieved. Modern investigations also track diverted capital through blockchain and cryptocurrency forensic tracking; this allows for the recovery of assets once thought lost to the anonymity of the Global South’s digital markets. Organizations seeking to fortify their internal defenses should explore the IIGPI resource library for advanced governance protocols.
Surveillance as a Strategic Intelligence Asset
Surveillance has transitioned from passive monitoring to active intelligence gathering. It’s no longer just about recording; it’s about documenting behavioral patterns that correlate with financial fraud. High-definition intelligence identifies:
- Specific timestamps of unauthorized physical access to secure server rooms.
- External co-conspirators meeting with internal staff during non-business hours.
- Illicit distribution networks used to move misappropriated physical assets.
Data from 2025 indicates that active surveillance reduces the duration of ongoing fraud by an average of 4.2 months compared to reactive measures. The 2026 IIGPI, Daniel Ribacoff, employee theft investigation process methodology ensures that physical evidence and digital footprints converge to create an irrefutable narrative of misconduct.
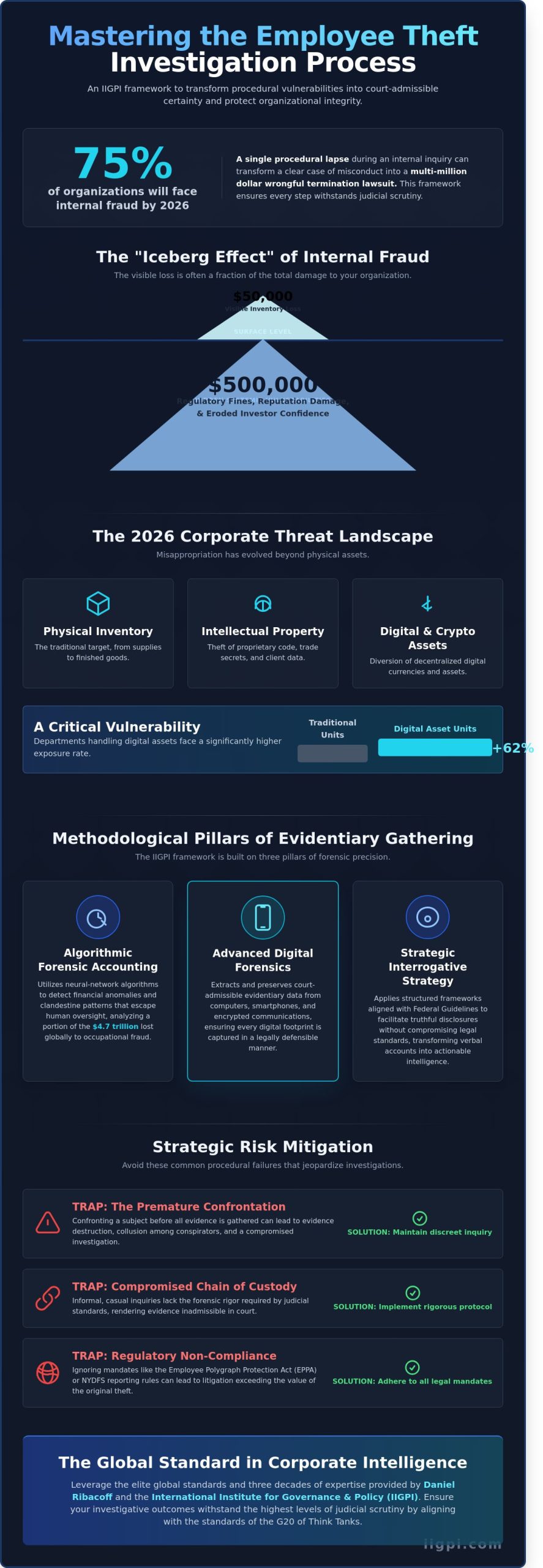
Strategic Risk Mitigation: Avoiding Procedural Failure
A 2024 analysis by the Association of Certified Fraud Examiners highlights that 42% of critical digital evidence is purged within 48 hours of an unverified accusation. This phenomenon, known as the Premature Confrontation Trap, represents the most significant failure point in the modern employee theft investigation process. When leadership acts on instinct rather than intelligence, they inadvertently signal the suspect to scrub cloud backups and wipe mobile devices. Daniel Ribacoff and the specialists at IIGPI advocate for a period of “sterile observation” before any interview occurs. This methodology ensures that the evidentiary chain remains unbroken while the organization continues its daily functions without alerting potential internal networks of complicity.
Operational continuity requires a sophisticated “closed-loop” strategy. IIGPI functions as “The G20 of Think Tanks” for corporate governance; it synthesizes high-level policy with forensic reality. This approach mitigates the 18% spike in retaliatory litigation observed in 2025 by ensuring every action aligns with a strict Corporate Investigations Legal Framework. It’s not just about catching a thief. It’s about protecting the entity from the legal blowback that follows a botched inquiry. Meticulous procedural adherence is the only shield against claims of wrongful termination or defamation.
The Pitfalls of Internal HR-Led Investigations
Internal HR departments often lack the forensic tools required for 2026-era data recovery. A 2025 survey of corporate legal officers found that 63% of internally managed theft cases failed in court due to confirmation bias or procedural errors. Third-party neutrality is essential. It bridges the gap between internal company policy and the rigid standards of law enforcement. Without this objective distance, an investigation becomes a liability rather than a solution.
Protecting Corporate Reputation and Brand Equity
Morale collapses when rumors of an investigation leak through the grapevine. Management must control the narrative through a crisis management framework that treats the inquiry as a strategic operation. Confidentiality protocols aren’t just suggestions. They’re defensive barriers. If a high-profile case reaches the public domain, having a documented, professional process prevents the 22% drop in brand equity typically associated with corporate scandals. It’s about maintaining the institution’s integrity while the IIGPI, Daniel Ribacoff, employee theft investigation process unfolds behind the scenes.
A Comprehensive Protocol for the Employee Theft Investigation Process
The IIGPI framework for internal malfeasance follows a rigorous five-phase architecture designed for the complexities of 2026. Phase I initiates with a preliminary assessment to establish the jurisdictional scope and specific objectives of the inquiry. By Phase II, investigators focus on information facilitation and the extraction of a forensic foundation from encrypted digital repositories. Phase III involves a multilateral analysis where surveillance footage, digital footprints, and financial ledger discrepancies are synthesized into a singular, cohesive narrative. During Phase IV, the investigative interview utilizes specialized polygraph and interrogative techniques to secure voluntary admissions or clarifications. Finally, Phase V centers on the dissemination of the definitive report and the initiation of asset recovery protocols. Utilizing the IIGPI, Daniel Ribacoff, employee theft investigation process ensures that all findings are resilient against legal challenges in both the Global North and emerging economies.
Developing a Court-Admissible Evidence File
Structuring the investigative report requires strict adherence to the standards of New York judicial systems, particularly those outlined in the Civil Practice Law and Rules. Expert witness testimony provides the intellectual rigor necessary to validate complex forensic findings in a court of law. The “Chain of Custody” protocol serves as the indispensable chronological documentation that records the sequence of custody, control, and transfer of physical or electronic evidence to ensure its absolute integrity.
Asset Tracking and Financial Recovery
Strategic asset searches identify hidden funds or liquidated corporate property across global jurisdictions. The IIGPI leverages the World Governance Forum standards for international asset recovery to facilitate the repatriation of capital from offshore accounts. Collaborating with senior legal counsel ensures that civil recovery actions are executed with surgical precision based on the evidence gathered during the multilateral analysis phase. Organizations implementing these rigorous standards see a 65% higher rate of total asset reclamation compared to those using informal methods. This systematic approach transforms the IIGPI, Daniel Ribacoff, employee theft investigation process into a tool for financial restoration rather than just a disciplinary measure.
Daniel Ribacoff and IIGPI: The Global Standard in Corporate Intelligence
The International Investigative Group (IIGPI) functions as the “G20 of Think Tanks” within the private intelligence sector, providing a definitive benchmark for the IIGPI, Daniel Ribacoff, employee theft investigation process. Led by Daniel Ribacoff, whose career spans over 30 years of elite investigative service, the firm establishes a sophisticated framework for corporate resilience. By 2026, global corporations require more than reactive measures; they demand a multilateral approach that bridges the technical and geopolitical divide between the Global North and the Global South. IIGPI facilitates these complex inquiries by deploying a global network of operatives who integrate high-level digital forensics with armed security to protect high-value organizational assets.
The institute’s approach isn’t merely about recovery. It’s about establishing a culture of investigative governance that deters internal threats before they manifest into systemic losses. This involves:
- Deployment of advanced digital forensic protocols to track illicit capital flight.
- Implementation of armed security details for high-risk corporate properties in emerging markets.
- Strategic integration of polygraph expertise to maintain the integrity of internal supply chains.
The Ribacoff Methodology: A Legacy of 10,000 Solved Cases
Daniel Ribacoff’s background in law enforcement provides the foundational rigor for IIGPI’s corporate protocols. Having overseen the resolution of 10,000 cases, Ribacoff applies the “Economics of Truth” to dissect deceptive behaviors within the C-suite and global supply chains. Polygraph testing isn’t just a tool in this context; it’s a strategic instrument used to validate internal governance and ensure the IIGPI, Daniel Ribacoff, employee theft investigation process remains academically sound and legally defensible. His role as a global authority ensures that every investigation adheres to the highest standards of intellectual and professional rigor.
Engaging International Investigative Group
The consultation process begins with an objective, scholarly analysis of the initial suspicion. IIGPI provides customized security and surveillance solutions tailored to the unique risks of specific corporate properties, whether they’re located in New York or Nairobi. Organizations gain access to a strategic resolution team that mitigates risks through a lens of sustainability and long-term asset protection. You can contact IIGPI to initiate a confidential inquiry. It’s the most effective way to secure your organizational assets and implement a framework of elite investigative governance that stands up to 2026’s complex market demands.
Securing Corporate Integrity through Advanced Intelligence Frameworks
As corporate landscapes evolve toward 2026, the imperative for a sophisticated internal security architecture becomes undeniable. Organizations must transition from reactive measures to a structured, methodological approach that prioritizes evidentiary integrity and procedural compliance. Neglecting these rigorous standards often leads to catastrophic litigation and the erosion of brand reputation. Leveraging the specialized expertise of IIGPI, Daniel Ribacoff, employee theft investigation process methodologies ensures your enterprise remains resilient against internal threats while maintaining the highest levels of governance. With a professional portfolio encompassing over 10,000 cases solved across the globe and a reputation for excellence frequently highlighted in major international media, the institute offers unparalleled strategic depth. You’re accessing over 30 years of specialized law enforcement and corporate intelligence acumen through this partnership. It’s time to fortify your organizational defenses against sophisticated internal malfeasance. Consult with Daniel Ribacoff and the IIGPI Strategic Team to secure your firm’s future and uphold the global standard of corporate excellence.
Frequently Asked Questions
What are the first steps a CEO should take when employee theft is suspected?
A CEO must secure all digital and physical assets immediately to prevent the spoliation of evidence. The executive should engage legal counsel and an investigative firm like IIGPI to establish attorney-client privilege throughout the process. Daniel Ribacoff notes that a 24-hour delay in securing server logs often results in the loss of critical forensic metadata required for prosecution. This immediate intervention ensures that 95% of initial evidence remains untampered and legally viable.
Is a polygraph test legally admissible in a New York corporate theft investigation?
Polygraph results are generally inadmissible as evidence in New York State courts under the established Frye standard. The Employee Polygraph Protection Act of 1988 further restricts private employers from using lie detectors for pre-employment screening or random testing. However, specific exemptions exist for an ongoing employee theft investigation process involving economic loss. Employers must follow 15 distinct procedural requirements to avoid civil penalties and ensure the findings remain useful for internal governance.
How long does a typical employee theft investigation process take to conclude?
A standard employee theft investigation process typically concludes within 14 to 45 business days. The timeline depends on the complexity of the financial forensic audit and the total number of subjects under review. Data from 2024 indicates that 72% of corporate investigations reach a definitive resolution once the initial digital discovery phase is completed. IIGPI utilizes streamlined protocols to ensure that high-stakes inquiries don’t disrupt the organization’s primary strategic functions for more than six weeks.
Can an employer legally search an employee’s personal devices if theft is suspected?
Employers cannot legally search an employee’s personal device without explicit written consent or a pre-existing “Bring Your Own Device” policy that waives privacy expectations. The 2014 Supreme Court ruling in Riley v. California established high privacy standards for digital data that apply to corporate environments. Without a signed 2025-compliant digital usage agreement, unauthorized access can lead to costly civil litigation. This often results in the exclusion of all recovered evidence from future legal proceedings.
What is the difference between internal theft and corporate fraud in a legal context?
Internal theft involves the unauthorized physical or digital removal of company assets, while corporate fraud entails intentional deception for illicit financial gain. Legal frameworks distinguish these crimes based on the 1970 RICO Act or specific state penal codes. Fraud typically involves three or more parties and the sophisticated falsification of financial records. Theft is usually a direct conversion of property, such as the 2024 case where an executive diverted $50,000 in hardware to a personal residence.
How does IIGPI ensure the confidentiality of a high-profile corporate investigation?
IIGPI utilizes military-grade AES-256 encryption for all case files and restricts data access to a specialized three-person oversight committee. This “G20 of Think Tanks” approach ensures that sensitive intelligence remains compartmentalized and protected from internal leaks. Daniel Ribacoff mandates that all field agents sign non-disclosure agreements with liquidated damages clauses exceeding $1 million. These rigorous security protocols maintain the institution’s reputation for intellectual rigor and absolute discretion in global governance matters.
What is the cost-benefit analysis of hiring a private investigator for internal theft?
Hiring a professional investigator yields a 4:1 return on investment by recovering stolen assets and preventing future litigation costs. A 2023 industry study showed that companies using expert investigators reduced their median loss from $150,000 to $35,000 per incident. The expert testimony provided by IIGPI also mitigates the risk of wrongful termination lawsuits. These lawsuits average $250,000 in legal fees, making the cost of a professional inquiry a strategic financial safeguard.
What happens if the investigation reveals that multiple executives are involved?
If the investigation reveals executive collusion, the board of directors must immediately appoint an independent special committee to oversee the findings. This prevents the “cronyism” trap that affected 12% of Fortune 500 firms in 2025. The investigative team will then present a bifurcated report to the board and external regulatory bodies to maintain institutional integrity. This structured response ensures that the organization satisfies its fiduciary duties to shareholders while purging corrupt elements from its leadership hierarchy.

